With almost everything in the world moving online, it’s no surprise that the risk of cyber threats has increased. Cybersecurity statistics show that the cost of cybercrime will reach $8 trillion in 2023 and increase to $10.5 trillion by 2025. One type of cyber threat that continues to take center stage in online security is botnet attacks, including denial of service attacks (DDoS) and phishing.
Botnets can launch enormous DDoS attacks on businesses, and recent data shows that they increased by 67% in 2022. These attacks are directly affecting companies’ bottom lines. One in four says that a single botnet attack costs their company an average of $500,000. If you’re a small or medium business owner, that’s not a cost you want to bear. Read on as we dive into the details of botnet attacks and give you a few examples to help you better understand this type of malicious cyberattack.
How Do Botnet Attacks Work?
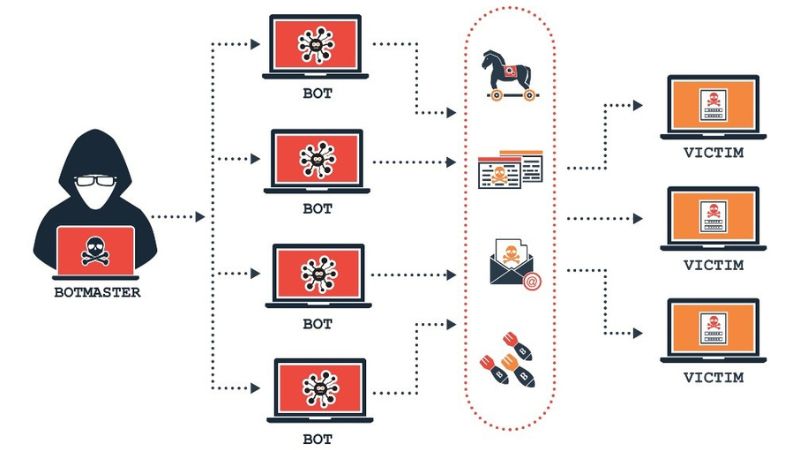
A botnet attack is a type of cyber-attack that involves the use of a group of internet-connected devices that have been compromised and are controlled by malicious actors. The term “botnet” comes from “robot network.” Essentially, it is a network of computers or other devices infected with malicious software (malware).
Attackers use these devices to carry out large-scale attacks on networks and systems. The purpose of these attacks is to steal data, crash servers, or spread malware.
The malware gives the attacker control over the infected devices, allowing them to send commands to the bots and use them for nefarious purposes. The most common botnet attacks include phishing, DDoS, brute force attacks, and device bricking.
3 Lessons Learned from the Misfortune of Others
Businesses, big and small, have been affected by botnet attacks. Yet another reason why it’s imperative to hire a company like TCI Technologies to oversee your cyber security needs. Here are a few examples of recent attacks to help illustrate the need to take action :
The AWS DDoS
On February 2020, Amazon Web Services (AWS) reported that they had mitigated a 2.3 terabytes-per-second (Tbps) attack, the largest DDoS attack ever seen.
The attack targeted an anonymous customer using a technique known as Connectionless Lightweight Directory Access Protocol (CLDAP) reflection. It used vulnerable third-party CLDAP servers to amplify the data directed toward a victim’s IP address by up to 70 times.
The AWS attack lasted for three days, but fortunately, Amazon’s AWS Shield service was able to mitigate the attack before any serious damage was done. While the damage was minimal, the attack could have had significant implications, including the hosting customers losing revenue and suffering brand image damage.
The Github Attack in 2018
This attack lasted 15 to 20 minutes and was estimated to be 1.3 terabits per second in size. It was carried out by hijacking Memcached servers. This distributed memory system is known for its speed and scalability, allowing attackers to amplify their attack by over 50,000 times its original size.
This amplification meant the attackers only needed to send a small amount of malicious data to generate enormous traffic toward GitHub’s servers. The attack was so powerful that it took GitHub offline for about 10 minutes.
The Microsoft Exchange Server Attack
The Microsoft Exchange Server Attack used four zero-day exploits of vulnerabilities in Microsoft Exchange to gain initial server access and plant web shell backdoors. This allowed the attackers to steal credentials, install malware, and gain continued access to the server.
The businesses most affected by this attack were small and medium-sized businesses that relied on Microsoft Exchange Server. Although there’s no mention of the extent of the damage, it’s safe to assume that any business affected lost confidential data or had their networks compromised as a result of this attack.
Stay on Top of Botnet Attacks
Overall, botnet attacks can have severe consequences for businesses of all sizes. Knowing the potential risks, you must take proactive measures to safeguard your company. Ensuring that all employees have access to up-to-date security information and seeking the expertise of a professional cybersecurity company are essential first steps.







