The thought of someone remotely taking control of your car while you’re driving, shutting down your brakes, or even tracking your every move, sounds like something out of a movie. But this is real life, and automotive hacking is the latest example of a cybersecurity vulnerability being exploited right now. In June 2024, KIA revealed that hackers could remotely take control of any of their cars built after 2013. It’s a clear reminder that as technology advances, the number of entry points for cybercriminals is expanding far beyond traditional computers. Everyday devices, including vehicles, are increasingly becoming potential targets.
Why Smart Cars Are Easy Targets for Hackers
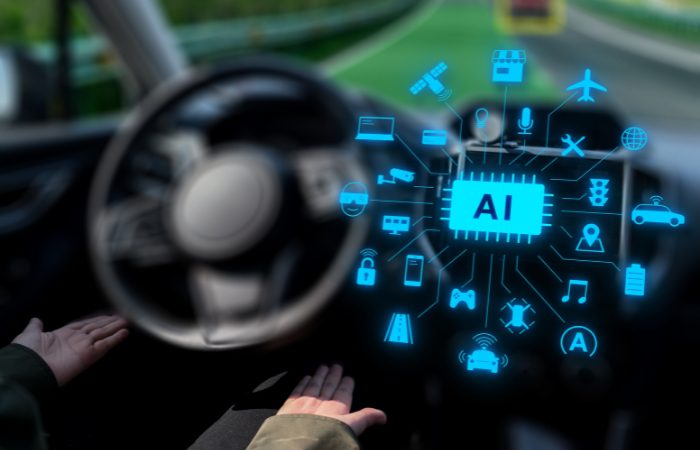
Modern cars are equipped with advanced technologies such as GPS, wireless connectivity, and autonomous driving features. But as vehicles get smarter, they also become more vulnerable to cyber threats. Constantly connected to the internet and equipped with numerous sensors and electronic control units, these vehicles offer multiple entry points for hackers, many of which are poorly secured.
The consequences of a breach can go far beyond inconvenience. A single vulnerability can put drivers, passengers, and entire fleets at serious risk.
Real-World Automotive Hacking Threat Examples
Below are some examples of how cyberattacks can compromise modern vehicles and the people who rely on them:
- Remote Control: Hackers have demonstrated the ability to remotely take control of a vehicle’s steering, brakes, and acceleration through vulnerabilities in connected systems.
- Data Theft: Personal data, including GPS locations, call logs, contact lists, and driving habits, can be extracted from a compromised vehicle.
- Ransomware: Just like on computers, hackers can lock down a car’s systems and demand a ransom to unlock them.
- Fleet Disruption: For businesses with connected fleets, a coordinated attack could simultaneously disable multiple vehicles, halting or ceasing operations.
The Broader Picture: A Growing IoT Threat

Automotive hacking is just one chapter in the wider narrative of IoT (Internet of Things) insecurity. From smart thermostats to medical devices and home security cameras, millions of connected devices are entering our lives and again, often with minimal built-in security.
The more connected you are, the more exposed you become. Every new IoT device is another potential opportunity for cyber criminals to put you or your company at risk of financial ruin.
6 Ways Individuals and Businesses Can Protect Themselves
1. Stay Informed and Vigilant
Understanding the risks is the first step. Be cautious about what data your car and other devices collect, as well as the permissions you grant to apps and services.
2. Keep Software Updated
Just like your phone or laptop, your car and IoT devices receive firmware updates that often include critical security patches. Don’t ignore them.
3. Secure Your Network
Ensure your home or business Wi-Fi is secure with strong passwords and up-to-date encryption. Many IoT hacks occur through poorly protected networks.
4. Segment Devices
On business networks, IoT devices should be isolated from critical systems whenever possible to minimize damage in the event of a breach.
5. Use Trusted Vendors
When selecting vehicles or devices, choose manufacturers that have proven cybersecurity practices and transparent update policies.
6. Bring in the Experts
Perhaps most importantly, consider working with cybersecurity professionals to assess and protect all your digital access points and assets.
When Everything’s Connected, Everything Needs Protection
Cybersecurity is as essential today as locking the front door of your building (especially if the lock is digital). As more devices connect to your network, the risks grow. From production assemblies to smart homes, vulnerabilities are everywhere, and attacks are constant.
Automotive hacking shouldn’t come as a surprise and serves as a powerful reminder of how real and immediate cyber threats have become.
TCI Technologies provides the expertise and tools to protect your systems with customized, enterprise-level security. Don’t wait. Contact us today to secure your network!